Instructure strikes deal with hackers who breached it twice
Instructure, the Salt Lake City-based educational technology giant and creator of the widely-used Canvas learning management system, announced on Tuesday that it has reached an agreement with ShinyHunters, the notorious financially motivated cybercrime group responsible for two significant breaches of its systems. This development follows a period of intense disruption for thousands of schools and educational institutions globally that rely on Canvas for their daily operations, managing everything from student coursework to critical staff data. The agreement, the financial terms of which remain undisclosed, reportedly involves the hackers providing evidence that the vast amount of stolen student and staff data has been destroyed, along with a commitment that Canvas customers will not face further extortion.
A Dual Assault on Digital Learning
The saga began with the initial breach on April 29, for which ShinyHunters swiftly claimed responsibility. The group asserted that they had compromised Canvas, a platform utilized by nearly 9,000 schools worldwide, and had stolen personal information pertaining to an astonishing 275 million individuals, encompassing both students and staff. The data purportedly included sensitive personal details, though the exact scope of the compromise was still under investigation by Instructure.
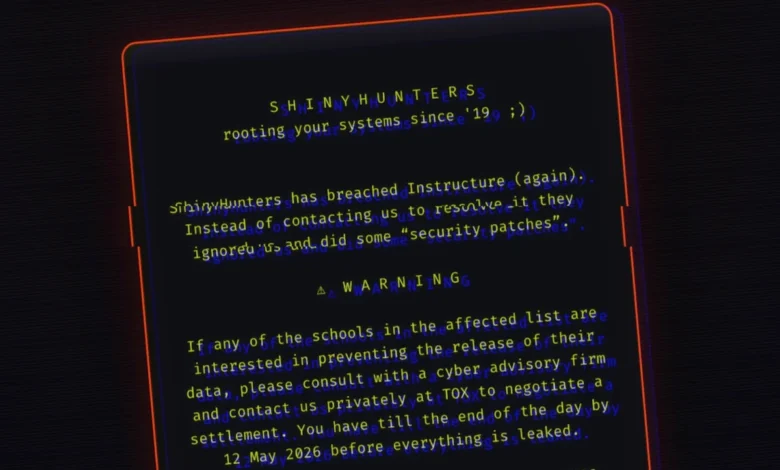
The situation escalated dramatically last week when ShinyHunters executed a second breach. This subsequent attack saw the cybercriminals deface Canvas login pages across numerous school websites, a clear and aggressive tactic designed to exert maximum pressure on Instructure to comply with their ransom demands. This act of public defacement served as a stark reminder of the hackers’ capabilities and their determination to force a payment. The disruption caused by these incidents rippled through the education sector, impacting countless students, educators, and administrators whose daily routines are intrinsically linked to the Canvas platform. From submitting assignments to accessing grades and communicating with peers and teachers, the integrity and availability of Canvas are paramount to modern education.
The Controversial Agreement and Data Destruction Claims
Late on Monday, Instructure publicly addressed the situation on its incident page, confirming the agreement with the perpetrators. The company stated that as part of this resolution, the hackers had furnished "evidence that the stolen data was destroyed," and that "Canvas customers would not be extorted." However, Instructure also issued a cautious disclaimer, acknowledging the inherent uncertainties in such negotiations, noting that there is "never complete certainty" when dealing with cybercriminals. Despite this caveat, the company emphasized that its customers should not feel compelled to engage directly with the hackers.
The precise financial details of the agreement remain shrouded in secrecy. Instructure has declined to disclose how much, if anything, was paid to ShinyHunters. Brian Watkins, a spokesperson for Instructure, did not respond to requests for comment or provide answers regarding the specifics of the agreement when contacted on Tuesday. The lack of transparency surrounding the payment raises significant concerns, particularly given the strong advisories from government agencies against paying ransoms.
Further corroboration of the agreement came from ShinyHunters itself. A post on their leak site, where the group typically threatens to publish stolen data if their demands are not met, was conspicuously removed as of Tuesday. This removal strongly indicated that a ransom payment had indeed been made, leading to the cessation of the publication threat. A representative from ShinyHunters reportedly told TechCrunch, "The data is deleted, gone. The company and its [sic] customers will not further be targeted or contacted for payment by us." This statement, while offering a semblance of closure, does little to alleviate the broader concerns surrounding the ethics and efficacy of ransomware payments.
Who are ShinyHunters? A Profile of a Persistent Threat
ShinyHunters is a prominent financially motivated cybercrime group that has gained notoriety for its large-scale data breaches and subsequent extortion attempts. Active for several years, the group specializes in compromising corporate networks, exfiltrating vast quantities of sensitive data, and then demanding payment, often in cryptocurrency, to prevent the public release or sale of the stolen information. Their modus operandi frequently involves exploiting vulnerabilities in systems to gain unauthorized access, followed by data exfiltration and then aggressive negotiation tactics, including public shaming and defacement, to pressure victims into paying. The group’s history includes breaches against various high-profile companies, underscoring their sophisticated capabilities and persistent threat to organizations across diverse sectors. Their involvement in the Instructure breach highlights the growing risk posed by such groups to critical infrastructure, particularly in the education sector which often possesses a trove of personally identifiable information.
The Perilous Precedent of Paying Ransom
Instructure’s decision to pay the hackers, if indeed a payment was made, places it in a controversial position. Governments worldwide, including the United States, have long and consistently urged victims of cybercrime not to pay ransoms. The rationale behind this stance is multifaceted: paying ransoms directly finances cybercriminal operations, encouraging future attacks and strengthening their capabilities. It creates a lucrative business model for these illicit enterprises, perpetuating a cycle of extortion. The FBI, for instance, in a statement last week that implicitly referenced the Instructure incident, advised victims "not send payment or respond" to the demands of cybercriminals.
Moreover, security researchers and law enforcement agencies frequently warn that victims cannot implicitly trust the word of malicious hackers. Numerous cases have demonstrated that cybercriminals, despite promising to delete stolen data upon payment, have been found to retain copies. This retained data can then be used for future extortion attempts, sold to other criminal groups, or otherwise exploited, leaving victims vulnerable even after they have paid. The LockBit ransomware group, for example, a prominent player in the cybercrime landscape, has been implicated in instances where data was not fully destroyed post-payment. This stark reality underscores the "never complete certainty" Instructure itself acknowledged, highlighting the inherent risks in negotiating with those who operate outside the bounds of law and ethics.
Echoes of PowerSchool: A Troubling Precedent
The Instructure incident bears an uncanny resemblance to a major cyberattack that targeted PowerSchool, another giant in the educational technology sector. In 2024, PowerSchool experienced a massive data breach that affected an estimated 70 million students and staff. Following the breach, PowerSchool also reportedly paid the hackers to secure the return and destruction of the stolen data. However, this payment did not guarantee immunity. Several of PowerSchool’s customers were subsequently extorted by a different crime group, which produced evidence of data from the original breach that had clearly not been destroyed.
This PowerSchool precedent serves as a grave warning for Instructure and its customers. It vividly illustrates the critical risk that even if Instructure’s agreement with ShinyHunters holds, there is no absolute guarantee that the data will not resurface, perhaps in the hands of other cybercriminals. The illicit trade of stolen data is a complex ecosystem, and information can be copied, sold, or leaked through various channels, making complete eradication exceedingly difficult, if not impossible, once it has left the victim’s controlled environment.
The Vulnerability of Educational Technology
The Instructure breach underscores the increasing vulnerability of the educational technology sector to sophisticated cyberattacks. As schools and universities have rapidly digitized their operations, particularly accelerated by the shift to remote learning, they have become repositories of vast amounts of sensitive personal data. This includes not only basic demographic information but also academic records, health details, financial aid data, and private communications between students and teachers. Such a rich trove of data makes EdTech platforms, like Canvas, incredibly attractive targets for financially motivated cybercriminals.
The impact of these breaches extends far beyond immediate operational disruption. For individuals, the exposure of personal information can lead to long-term risks such as identity theft, phishing scams, and targeted social engineering attacks. For educational institutions, it can result in significant financial costs related to incident response, forensic investigations, legal fees, credit monitoring services for affected individuals, and potential regulatory fines. Furthermore, such incidents erode trust among students, parents, and staff in the ability of institutions and their technology providers to safeguard sensitive information. The FBI’s Cyber Division, acknowledging the widespread system disruptions affecting schools, has repeatedly stressed the importance of robust cybersecurity measures and incident response planning within the education sector.
The Scope of Compromised Information
The data reportedly stolen from Instructure, some of which TechCrunch has had sight of, paints a concerning picture of the potential ramifications for those affected. It includes students’ names, their personal email addresses, and critically, messages exchanged between teachers and students. These messages can often contain highly private and personal information, ranging from academic struggles and mental health concerns to disciplinary issues and personal disclosures. The compromise of such intimate communications not only constitutes a significant privacy violation but also opens individuals up to potential blackmail, reputational damage, or highly personalized phishing attacks designed to extract further information or exploit vulnerabilities. The sheer volume of data claimed by ShinyHunters – 275 million records – suggests an unprecedented scale of exposure for the education community.
Instructure’s Internal Response and Accountability
In its public statements, Instructure acknowledged that its systems had been breached twice within a year. However, the company maintained that these two incidents were "distinct events" involving "different systems." While this differentiation might imply separate vulnerabilities or attack vectors, it also raises questions about the overall security posture and resilience of Instructure’s infrastructure. Two significant breaches in such close proximity, regardless of their distinct nature, signal a potential systemic challenge in identifying, mitigating, and preventing sophisticated cyber threats.
The ongoing investigation by Instructure is crucial for fully understanding the root causes of these breaches and implementing robust preventative measures. However, a notable aspect of Instructure’s response has been the lack of clarity regarding internal accountability. When questioned by TechCrunch, Instructure declined to comment on who within the company is responsible for cybersecurity oversight, or whether its chief executive, Steve Daly, plans to resign following these major data security failures. This silence on leadership accountability can further undermine confidence and trust, both among customers and the wider public, in the company’s commitment to prioritizing cybersecurity.
Navigating the Aftermath and Future Security Challenges
The agreement with ShinyHunters, while providing an immediate cessation of public threats, marks only the beginning of a long and complex recovery process for Instructure and the institutions that rely on Canvas. Schools and districts must now grapple with the uncertainty surrounding the true fate of the stolen data and remain vigilant for any signs of future extortion attempts, even from different criminal groups. This necessitates proactive monitoring, enhanced security protocols, and clear communication strategies to inform and protect affected students and staff.
For Instructure, the path forward involves not only validating the destruction of data but also undertaking a comprehensive review and overhaul of its cybersecurity defenses. This includes investing in advanced threat detection, strengthening access controls, regular security audits, and fostering a culture of cybersecurity awareness throughout its organization. The incident serves as a critical wake-up call for the entire EdTech industry, highlighting the urgent need for heightened security standards, greater transparency in incident response, and a collaborative approach to combating cybercrime that specifically targets the sensitive data within educational ecosystems. The long-term implications for Instructure’s brand reputation and market position will heavily depend on its ability to rebuild trust and demonstrate an unwavering commitment to protecting the digital lives of millions of students and educators.