The Digital Double How Global Bad Actors Are Impersonating Investigative Journalists to Harvest Intelligence
The landscape of modern espionage has shifted from the shadows of physical surveillance to the encrypted corridors of private messaging applications, where the latest weapon of choice is the identity of the investigative journalist. Recent reports from ProPublica and other international news organizations highlight a sophisticated and growing trend of "digital doubling," where bad actors—often suspected of having ties to state-sponsored intelligence agencies—assume the personas of high-profile reporters to extract sensitive information from government officials, military contractors, and activists. Unlike traditional "pig butchering" scams that target financial assets, these operations are designed for high-level intelligence gathering, leveraging the hard-earned trust that journalists build with their sources to bypass traditional security barriers.
The Mechanics of a Targeted Impersonation Campaign
The phenomenon gained significant attention following a series of incidents involving Robert Faturechi, an award-winning investigative reporter for ProPublica. The operation followed a precise pattern of social engineering. In the first instance, an official with the Canadian military received messages on WhatsApp from a person claiming to be Faturechi. The impostor used a Miami-based phone number and Faturechi’s official professional headshot as a profile picture. The "Fake Robert" attempted to solicit information regarding the official’s work, which involved international relations and defense matters concerning Ukraine.
Two weeks later, a second incident surfaced involving a Latvian businessman who coordinates drone (UAV) development and equipment logistics for the Ukrainian military. The businessman was approached on Signal, a platform favored by journalists for its end-to-end encryption. The impostor again used Faturechi’s likeness and professional credentials to ask specific questions about the application of UAV technology in the Ukrainian theater of war. When the businessman requested a phone or video call to verify the reporter’s identity, the impostor demurred, citing security "discomfort," and instead attempted to lure the target into a phishing scheme designed to compromise his email account.
These cases are not isolated. They represent a broader tactical shift in how intelligence is gathered in the 21st century. By posing as a member of the press, an attacker can ask probing, sensitive questions under the guise of "research" or "fact-checking," which might otherwise trigger internal security alarms if the same questions were asked by a stranger or a competitor.
Chronology of the Investigative Journalist Impersonation Trend
The rise of journalist impersonation has followed a distinct timeline, escalating in complexity over the last several years:

- October 2016: In one of the most consequential precursors to modern digital impersonation, John Podesta, chairman of Hillary Clinton’s presidential campaign, fell victim to a phishing email. While the attacker did not pose as a journalist, the incident demonstrated how a simple "security alert" could lead to the theft of thousands of sensitive documents, setting the stage for the use of fake identities to breach high-value targets.
- Early 2023: Reuters reported that two of its journalists based in China were being impersonated on Instagram and Telegram. The fake accounts targeted activists protesting the Chinese government’s "Zero-COVID" policies, attempting to identify organizers and participants.
- January 2024: The German government issued a formal warning regarding state-sponsored actors attempting to hijack the Signal accounts of European officials and members of the press.
- March 2024: The FBI’s Internet Crime Complaint Center (IC3) issued a Public Service Announcement regarding Russian intelligence actors. These individuals were found to be posing as Signal’s security department to trick American officials and journalists into revealing account-takeover information.
- April 2024: ProPublica’s Robert Faturechi documented the specific attempts to use his identity to target defense officials in Canada and drone developers in Latvia.
- May 2024: A Reuters correspondent in Saudi Arabia, Timour Azhari, issued a public warning after discovering a WhatsApp account using his name and photo to contact sources in the Middle East.
Supporting Data: The Privacy Paradox of Encrypted Messaging
The very features that make apps like Signal and WhatsApp essential for journalism also make them fertile ground for impersonators. Signal, by design, retains almost no metadata. It knows only when an account was created and the phone number associated with it. It does not track who a user is messaging, nor does it store message content.
According to data from the Electronic Frontier Foundation (EFF), the adoption of Signal has surged among the general public, but this popularity has attracted more sophisticated attackers. Cooper Quintin, a technologist at the EFF, notes that as Signal becomes a "standard" for secure communication, attackers view it as a high-value platform for phishing.
Current technical data on these attacks suggests several key trends:
- Low Barrier to Entry: Creating a fake profile requires only a VOIP (Voice Over IP) number and a publicly available image.
- Platform Limitations: Because Signal cannot see the content of messages, it cannot automatically flag suspicious links or behavioral patterns in the same way that unencrypted platforms like Facebook or Gmail can.
- Verification Gap: Unlike X (formerly Twitter) or Meta platforms, Signal does not have a "verified" badge system for journalists, primarily because the staffing and data collection required for such a system would undermine the app’s core privacy mission.
Official Responses and Institutional Reactions
News organizations and tech platforms have begun to respond to this threat, though their methods vary. A spokesperson for WhatsApp stated that the company utilizes automated systems to ban accounts that display suspicious behavior, such as attempting to open multiple accounts from a single location or sending high volumes of messages to non-contacts. However, the company acknowledged that once a user is blocked, they often simply move to a different platform or use a different number.
Digital security expert Runa Sandvik, who advises newsrooms on threat mitigation, emphasizes that the burden of verification is increasingly falling on the sources themselves. Sandvik argues that journalists must now be proactive in publicizing their official contact methods. "If and when impersonation happens, be very public about it," Sandvik advised. "Let people know this is happening so if they hear from you, they know what to look out for."
The FBI and the German Federal Office for Information Security (BSI) have both released guidance urging high-profile individuals to use "safety numbers" or "security codes" on Signal. These are unique strings of numbers that allow two parties to verify that their conversation is encrypted and that neither party’s device has been swapped or intercepted.

Analysis of Implications for Press Freedom and Global Security
The implications of these impersonation campaigns extend far beyond the reputation of individual reporters. They strike at the heart of the "leap of faith" required for whistleblowers to come forward. Investigative journalism relies on the willingness of individuals to share information—often at great personal or professional risk—under the assumption of confidentiality and the legitimacy of the recipient.
The Erosion of Public Trust
When bad actors use the guise of the press to conduct espionage, they contribute to a general atmosphere of paranoia. If a potential source cannot be certain that the person on the other end of an encrypted chat is a legitimate reporter, they are significantly less likely to share documents or testimony that could expose corruption or human rights abuses. This "chilling effect" serves the interests of authoritarian regimes and corrupt entities that benefit from a lack of transparency.
Shift in Intelligence Tactics
The move from technical hacking (exploiting software vulnerabilities) to social engineering (exploiting human trust) suggests that security software has become robust enough that the "human element" is now the weakest link. By using a journalist’s identity, an intelligence officer can bypass the need for expensive "zero-day" exploits. They simply ask for the information, and frequently, they receive it.
The Geopolitical Dimension
The specific targeting of individuals involved in the Ukraine conflict—such as the drone developers in Latvia and military officials in Canada—points toward a geopolitical motive. These are not "scammers" in the traditional sense; they are likely state-aligned operatives seeking tactical advantages on the battlefield or insight into Western military support structures.
Verification Best Practices for Sources and Officials
To combat this trend, major newsrooms including ProPublica, The New York Times, and Reuters have standardized their verification protocols. Experts recommend that any official or source contacted by a journalist via a messaging app should take the following steps:
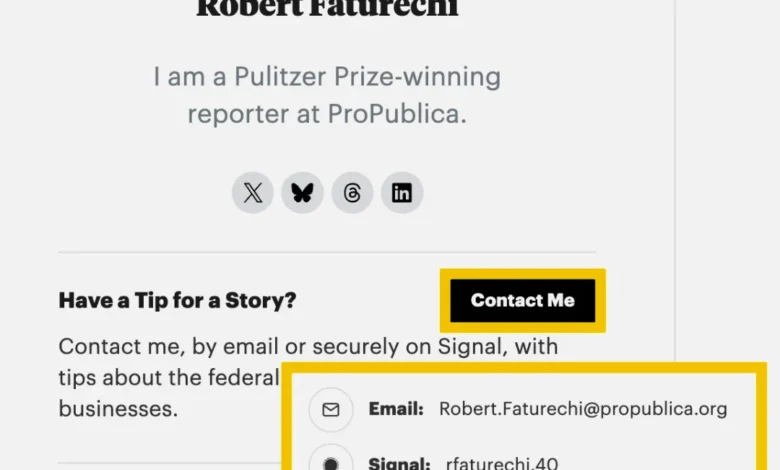
- Check Official Bios: Most major news organizations host staff bio pages that include verified Signal handles, WhatsApp numbers, or PGP keys. If the number contacting you does not match the one listed on the official
propublica.orgornytimes.comstaff page, it is likely a scam. - Request an Email: Every legitimate reporter has an official company email (e.g.,
[email protected]). Ask the person to send a confirmation email from that address. - Cross-Platform Verification: If contacted on Signal, reach out to the reporter via their verified social media profile (such as a LinkedIn or X account with a long history) to confirm they are the one messaging.
- Beware of Technical Requests: Legitimate journalists will never ask a source to click a link to "verify their identity" or provide a login code for an email or messaging account.
As the digital frontier continues to evolve, the identity of the journalist remains a valuable asset—not just for the pursuit of truth, but for those who wish to subvert it. The defense against these "digital doubles" requires a combination of technical vigilance, institutional transparency, and a renewed commitment to the protocols of verification that have always been the bedrock of professional journalism.