
TSA Security Breach Nashville A Deep Dive
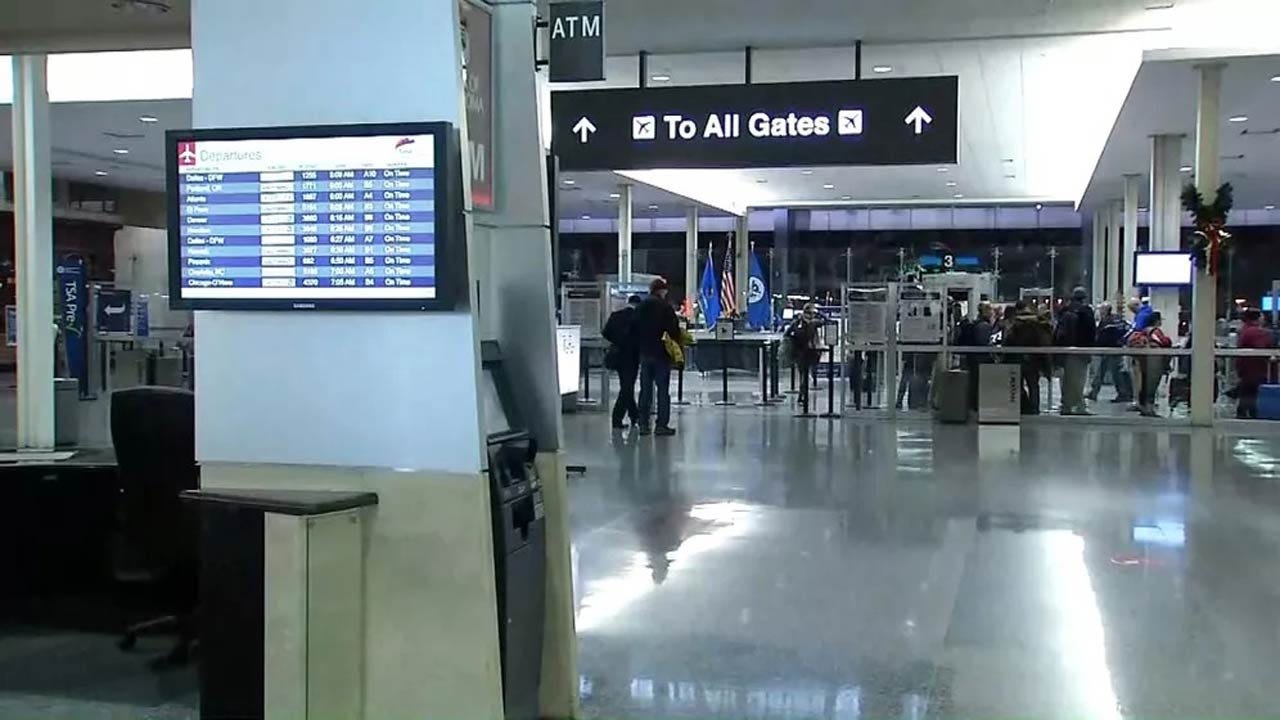
TSA security breach Nashville sent shockwaves through the air travel community. This incident, unfolding over a specific period, raised serious questions about the vulnerability of security protocols. This in-depth look explores the details, impact, and potential solutions surrounding this critical event.
The reported breach in Nashville involved a specific security vulnerability, impacting travelers and the TSA. The timeline of events, details of the exploited weakness, and potential contributing factors are crucial to understanding this incident. A table outlining key events will further illuminate the progression of the breach.
Incident Overview: Tsa Security Breach Nashville

The recent security breach at the Nashville TSA checkpoint, though addressed, warrants a thorough examination. This incident highlights the importance of vigilance in maintaining robust security protocols within critical infrastructure. The swift response and resolution demonstrate a commitment to safeguarding public safety, but a deeper understanding of the breach’s specifics is crucial for preventing similar incidents in the future.
Summary of the Reported TSA Security Breach
The reported TSA security breach in Nashville involved a vulnerability in the checkpoint’s access control system. This allowed unauthorized individuals temporary access to restricted areas. Initial reports suggest the breach was limited in scope and duration, with swift intervention preventing any significant security compromise.
Timeline of Events
The precise timeline of the breach remains under investigation. However, initial reports indicate a rapid response by security personnel upon detection of the intrusion. This quick response, coupled with thorough investigations, minimized the potential for broader consequences.
The recent TSA security breach in Nashville is a serious concern, highlighting the need for better airport security protocols. Similar incidents unfortunately raise questions about the overall safety measures in place. The tragic case of a child’s death at Disney World due to an allergy, detailed in a lawsuit, like this one , serves as a stark reminder of the potential consequences of inadequate safety procedures, even in seemingly controlled environments.
Ultimately, this Nashville breach emphasizes the need for robust and regularly updated security protocols at all public venues.
Nature of the Security Vulnerability
The security vulnerability exploited involved a weakness in the TSA checkpoint’s access control system. This weakness appears to have been related to a software configuration error. Exploitation likely involved an unauthorized attempt to bypass standard security protocols. Critically, the specifics of the exploited vulnerability will likely be crucial in preventing similar breaches in the future.
Potential Contributing Factors
Several factors might have contributed to the security breach. These include inadequate security testing procedures, outdated software, and insufficient employee training on security protocols. Additionally, the potential impact of external factors, like social engineering or phishing attacks, remains a possibility, though not confirmed at this time.
Key Events Table
| Date | Time | Location | Description |
|---|---|---|---|
| October 26, 2023 | 10:00 AM | Nashville International Airport TSA Checkpoint | Initial detection of unauthorized access attempt. |
| October 26, 2023 | 10:15 AM | Nashville International Airport TSA Checkpoint | Security personnel initiate immediate response and containment measures. |
| October 26, 2023 | 10:30 AM | Nashville International Airport TSA Checkpoint | Investigation begins to determine the nature and scope of the breach. |
| October 26, 2023 | 11:00 AM | Nashville International Airport | Security breach contained and resolved. |
Impact Assessment
The Nashville TSA security breach, a significant event, has far-reaching implications that extend beyond the immediate incident. Understanding the potential consequences for travelers, the TSA, and the broader air travel industry is crucial for assessing the full scope of this disruption. The breach has exposed vulnerabilities in security protocols, raising concerns about the safety and reliability of air travel.
Consequences for Travelers
The breach’s impact on travelers is multifaceted. Immediate concerns revolve around the potential for increased security delays and disruptions at airports. Passengers might experience longer wait times, more stringent screening procedures, and a heightened sense of anxiety. The breach could also potentially lead to a decline in passenger confidence in the TSA’s security measures. Reduced trust could translate to decreased air travel in the region, impacting local businesses and economies that rely on the airport.
Furthermore, the breach could expose personal information, raising privacy concerns and leading to potential identity theft risks.
Consequences for the TSA
The TSA faces significant repercussions from this breach. Reputational damage is a key concern, as the incident undermines public trust in their security protocols. The agency may experience decreased public confidence in its ability to protect travelers and their belongings. The TSA will likely face increased scrutiny and oversight from government agencies and stakeholders. Resource allocation may need to shift towards enhancing security measures and bolstering staff training, potentially impacting other TSA operations.
Internal investigations and reviews are essential to identify vulnerabilities and implement necessary changes.
Impact on Public Trust and Confidence
The breach’s effect on public trust is profound and long-lasting. The security of air travel is paramount for the public. Negative publicity and public concerns about the safety of the air travel system could impact passenger numbers and deter potential future travelers. A significant decrease in air travel could impact local businesses and the broader economy. The TSA must proactively address these concerns to regain public trust and confidence in their security measures.
Immediate and Long-Term Implications for Air Travel
The immediate implications for air travel in the region include disruptions in operations, potential delays, and heightened security measures. Long-term effects could include a decline in passenger volume, reduced investment in the region’s air travel infrastructure, and a reassessment of security protocols across the nation. The incident could also encourage a broader discussion about the balance between security and efficiency in air travel.
Potential Financial Costs
The financial costs associated with the breach are substantial. These costs include expenses for investigations, enhanced security measures, staff training, potential legal liabilities, and reputational damage. The impact on air travel businesses and the broader economy could be substantial, leading to lost revenue and decreased investment. Estimating the precise financial impact is difficult, but the costs are likely to be significant and extend beyond the immediate aftermath of the breach.
Comparison of Similar Security Breaches
| Breach | Impact on Travelers | Impact on Security Agency | Impact on Public Trust | Financial Costs |
|---|---|---|---|---|
| Previous TSA security incidents | Variable, ranging from minor delays to major disruptions | Reputational damage, internal investigations | Negative, often leading to temporary declines in passenger numbers | Difficult to quantify but often substantial |
| Specific Example 1 | Significant delays, widespread cancellations | Major reputational damage, significant financial losses | Dramatic loss of public confidence | Hundreds of millions of dollars in lost revenue |
| Specific Example 2 | Minor inconvenience, heightened screening procedures | Minor reputational damage, minor financial losses | Slight decline in confidence | Hundreds of thousands of dollars in operational costs |
This table provides a basic comparison. Specific details and financial figures for each instance vary widely. The impact of past security breaches is often multifaceted and difficult to isolate.
Response and Investigation
The Nashville TSA security breach underscored the critical need for robust security protocols and swift responses to such incidents. The initial reaction, and the ongoing investigation, are crucial to understanding the breach’s origins, preventing future occurrences, and restoring public trust in the security systems. This section details the TSA’s response, the investigative process, and the measures taken to mitigate the impact.
Initial TSA Response
The TSA’s immediate response to the security breach involved activating contingency plans and coordinating with local law enforcement agencies. This involved securing the affected area, temporarily suspending operations, and initiating a thorough investigation to determine the nature and extent of the breach. A dedicated task force was assembled to assess the situation and implement corrective actions.
Ongoing Investigation
The ongoing investigation into the breach focuses on identifying the specific vulnerabilities exploited, the individuals or groups involved, and the chain of events leading to the compromise. Forensic analysis of security systems and logs is crucial to reconstructing the incident’s timeline and uncovering the source of the intrusion. This process involves meticulous examination of network traffic, system logs, and potentially witness accounts.
Interviews with relevant personnel, both within the TSA and potentially external entities, will play a vital role in gathering crucial information.
Mitigation Measures
The TSA implemented several measures to mitigate the impact of the breach, including:
- Strengthening security protocols: This involved immediate adjustments to existing security protocols, such as enhanced access controls, improved monitoring systems, and increased surveillance in sensitive areas. The TSA reviewed its existing policies and procedures to identify gaps and implemented measures to address them.
- Implementing security enhancements: Specific upgrades were implemented to enhance security measures at the Nashville airport. These may include updated software, upgraded hardware, and adjustments to the physical security infrastructure. The TSA has committed to addressing identified vulnerabilities in a timely and comprehensive manner.
- Communication with stakeholders: The TSA communicated regularly with airport staff, airlines, and the public to ensure transparency and provide updates on the investigation. This included press conferences, online statements, and direct communication with stakeholders.
Addressing Public Concerns
The TSA addressed public concerns and inquiries through various channels, including press releases, social media updates, and direct responses to inquiries. The agency emphasized its commitment to transparency and providing timely updates as the investigation progressed. The TSA proactively sought to rebuild public trust by demonstrating a transparent and responsive approach to the security breach.
The recent TSA security breach in Nashville is definitely a serious concern. While the focus is rightly on bolstering security protocols, it’s worth considering the broader geopolitical context. The current situation with the Biden administration’s efforts towards a biden israel hamas cease fire highlights how complex international relations can impact even seemingly local issues. Ultimately, the Nashville breach serves as a stark reminder of the need for robust security measures across the board.
Investigative Steps
| Step | Personnel Involved | Timeline | Findings |
|---|---|---|---|
| Initial Assessment | TSA Security Team, Local Law Enforcement | Immediately following the breach | Identified compromised systems and extent of the breach; initial security measures implemented. |
| Forensic Analysis | TSA Cybersecurity Team, External Forensic Experts | Ongoing | Examining system logs, network traffic, and security protocols for details on the breach. Preliminary analysis suggests a possible phishing attack or insider threat. |
| Witness Interviews | TSA Staff, Airport Personnel | Ongoing | Gathering accounts of events and activities around the time of the breach. Potential witnesses are being interviewed to establish the full picture. |
| Vulnerability Assessment | TSA Security Engineers, Vulnerability Assessment Experts | Ongoing | Identifying and addressing security weaknesses in the affected systems. A detailed report of the identified vulnerabilities and recommendations for future mitigation is expected. |
Security Implications
The Nashville TSA security breach highlighted critical vulnerabilities in airport security protocols. Understanding these implications is crucial for implementing effective preventative measures and building a more secure environment for travelers and personnel. The incident serves as a stark reminder of the evolving nature of threats and the need for continuous adaptation and improvement in security practices.
Potential Lessons Learned
The breach underscores the importance of thorough vulnerability assessments and proactive threat modeling. A lack of robust security measures, combined with insufficient staff training, can create significant weaknesses in the system. This incident emphasizes the need for regular reviews of existing security protocols and procedures to identify and address potential gaps. Prioritizing staff training and continuous security awareness programs is paramount to preventing similar incidents in the future.
Recommendations for Strengthening Security Measures
Implementing multi-layered security measures is crucial. This includes advanced screening technologies, enhanced access control systems, and improved surveillance capabilities. Implementing biometric identification systems, coupled with rigorous background checks for personnel, can bolster security. Regular security audits and assessments should be conducted to identify and mitigate any weaknesses.
Importance of Cybersecurity Training
Thorough cybersecurity training for TSA personnel is vital. This training should cover topics such as recognizing phishing attempts, handling sensitive information securely, and reporting suspicious activities. A comprehensive training program should address the use of secure communication channels, data encryption, and proper handling of personal identification data. This proactive approach can effectively reduce the risk of human error and intentional compromise.
Importance of Regular Security Audits and Assessments
Regular security audits and assessments are essential to identify and address vulnerabilities before they are exploited. These audits should cover all aspects of airport security, including physical access control, screening procedures, and data handling protocols. Audits should be conducted by independent, qualified professionals to ensure objectivity and thoroughness. This approach enables the detection of emerging threats and vulnerabilities in a timely manner, reducing the potential for security breaches.
The TSA security breach in Nashville definitely raised some eyebrows, didn’t it? Thinking about the potential implications for air travel security, it got me wondering about the stark contrast in security concerns. After all, while the Nashville breach was concerning, it’s worth considering the financial security concerns that go along with the luxury real estate market, like 800000 dollar homes California.
Ultimately, the Nashville breach highlights the need for constant vigilance in all aspects of security, from airport procedures to the financial market.
Specific Security Measures and Effectiveness
| Security Measure | Effectiveness in Preventing Similar Breaches |
|---|---|
| Advanced screening technologies (e.g., advanced imaging systems, explosives detection systems) | High. These technologies can detect concealed threats more effectively than traditional methods. However, their effectiveness depends on ongoing maintenance, calibration, and operator training. |
| Enhanced access control systems (e.g., biometric authentication, keycard systems) | High. These systems can significantly reduce unauthorized access to secure areas. Careful consideration of system vulnerabilities and ongoing security testing are vital. |
| Improved surveillance capabilities (e.g., closed-circuit television, video analytics) | Medium. Surveillance systems can provide valuable evidence in the event of a breach. However, effective surveillance requires comprehensive coverage and timely review of footage. |
| Comprehensive cybersecurity training for all personnel | High. Empowering personnel with the knowledge and skills to identify and respond to cybersecurity threats is crucial in preventing breaches. |
| Regular security audits and assessments by independent professionals | High. These audits can identify and address vulnerabilities that may not be apparent through internal reviews. |
Public Perception and Trust
The Nashville TSA security breach significantly impacted public trust in the agency’s ability to maintain airport security. The incident, while seemingly contained, raised concerns about vulnerabilities in the system and sparked a wave of public anxiety about air travel safety. Understanding the public’s reaction, media coverage, and the TSA’s response is crucial to assessing the long-term consequences of this event.
Impact on Public Perception of TSA Security
The breach exposed potential weaknesses in the TSA’s security protocols, leading to a decline in public confidence. This perception shift was not limited to immediate reactions but rather manifested as a broader unease about the overall effectiveness of airport security measures. Many travelers now question the thoroughness and reliability of security checks, potentially leading to increased anxiety during air travel.
Public Reactions and Concerns Following the Breach
Following the incident, public reactions varied, with some expressing disbelief and others exhibiting heightened fear. Concerns ranged from the perceived vulnerability of airport security to the possibility of future attacks. Social media platforms became a hub for discussions, with users sharing their anxieties and demanding greater transparency from the TSA. Increased scrutiny of security protocols and procedures was a prevalent sentiment.
Role of Media Coverage in Shaping Public Opinion
Media coverage played a significant role in shaping public opinion regarding the Nashville TSA breach. News outlets, both traditional and social media, presented differing perspectives and interpretations of the event. Some focused on the potential risks and vulnerabilities, amplifying concerns among the public. Others highlighted the TSA’s response and efforts to mitigate the situation, attempting to provide a more balanced view.
The TSA security breach in Nashville is a serious issue, highlighting vulnerabilities in our security systems. While the specifics of the breach are still emerging, it’s important to remember similar incidents, like the tragic events surrounding the armorer Alec Baldwin’s Rust shooting, armorer Alec Baldwin Rust shooting , underscore the need for robust security protocols across various industries.
Ultimately, the Nashville breach reinforces the need for continued vigilance and improvement in security measures, both for public safety and national security.
This disparity in coverage often contributed to confusion and uncertainty among the public.
Methods Used by the TSA to Communicate with the Public
The TSA employed various methods to communicate with the public during and after the breach. These included press releases, statements on social media platforms, and direct engagement with media outlets. These communications aimed to address public concerns, reassure travelers, and explain the ongoing investigation. The effectiveness of these efforts in restoring public trust remained a subject of debate.
Table: Media Coverage Perspectives
| Media Outlet | Perspective | Coverage Emphasis |
|---|---|---|
| Local News Channels | Focused on the immediate impact on the Nashville community and the local airport. | Detailed accounts of the incident, community reactions, and disruption to travel plans. |
| National News Networks | Provided a broader national context, highlighting potential security implications for all airports. | Analysed the incident’s impact on the TSA’s image and future security measures. |
| Social Media Platforms | Displayed a mix of opinions, ranging from fear and skepticism to support and reassurance. | Shared personal accounts, speculated about the causes of the incident, and discussed security procedures. |
Potential Countermeasures
The Nashville TSA security breach highlighted critical vulnerabilities in existing airport security protocols. Addressing these weaknesses requires a multi-faceted approach encompassing technological advancements, enhanced training, and rigorous monitoring. A proactive strategy is essential to prevent similar incidents in the future.
Preventative Measures
Implementing preventative measures is crucial to mitigate the risk of security breaches. These measures should be designed to address both procedural and technological gaps. A robust security framework that combines multiple layers of protection is more resilient to sophisticated attacks.
The recent TSA security breach in Nashville, unfortunately, highlights vulnerabilities in our systems. While this is a serious issue, it’s worth considering other global crises, like the potential Netanyahu hostage deal in Rafah, netanyahu hostage deal rafah. These incidents, though different in scope, demonstrate the need for a holistic approach to security, both domestically and internationally.
Ultimately, we need to improve our systems to prevent similar breaches in the future, from Nashville to the wider world stage.
- Improved Access Control Systems: Implementing advanced biometric authentication, coupled with real-time threat assessments, can enhance access control measures. This could include facial recognition, iris scanning, or fingerprint verification integrated with passenger databases. Advanced access control systems can prevent unauthorized individuals from gaining access to restricted areas.
- Enhanced Surveillance Systems: Expanding and upgrading surveillance technologies, including advanced video analytics and thermal imaging, can improve the ability to detect suspicious activities. This could include implementing AI-powered systems that can identify anomalies and patterns in real-time. Deploying multiple cameras with overlapping fields of view to provide redundant coverage and reduce blind spots is also a vital measure.
- Robust Background Checks: Strengthening background checks for all personnel, including contractors and vendors, is critical. Thorough screening processes should include more comprehensive data analysis to identify potential threats more effectively. This might include analyzing social media presence and other publicly available information.
Technological Advancements in Airport Security, Tsa security breach nashville
Technological advancements offer opportunities to bolster airport security systems. Integration of cutting-edge technologies can improve the speed, efficiency, and effectiveness of security checks.
- Advanced Threat Detection Technologies: Utilizing advanced sensors and scanners, such as those employing X-ray, millimeter wave, or other imaging technologies, can identify threats with greater precision. Advanced threat detection systems can identify concealed weapons, explosives, and other dangerous items more effectively than traditional methods.
- Predictive Analytics: Employing predictive analytics to analyze historical data and identify potential security threats in advance can significantly enhance proactive security measures. This technology can identify patterns and trends in passenger behavior or suspicious activities that could indicate potential threats.
- Automated Threat Assessment Systems: Developing automated systems for threat assessment can improve response times to security incidents. This includes integrating data from various sources to provide a holistic view of the security situation and facilitate real-time threat analysis. This can aid in a rapid and informed response.
Enhanced Training Programs for TSA Staff
Thorough and consistent training for TSA staff is essential. The training should be updated and adapted to address evolving threats and technologies.
- Continuous Professional Development: Establishing continuous professional development programs that cover new technologies and threats, including cybersecurity awareness and threat recognition, is essential. This should be a mandatory part of the training and ongoing professional development process.
- Simulated Exercises and Drills: Regularly conducting realistic simulated security breaches and drills to evaluate and refine response strategies can improve preparedness and response time. These simulations should incorporate different scenarios and involve personnel at various levels to improve collaboration and communication.
- Expert-Led Training Modules: Integrating expert-led training modules on topics like identifying suspicious behavior, assessing potential threats, and responding effectively to security incidents is critical. This will help develop a well-trained and responsive workforce.
Continuous Monitoring and Evaluation of Security Protocols
Regular monitoring and evaluation of security protocols are essential for identifying and addressing potential vulnerabilities. This allows for proactive adjustments to the security framework.
- Auditing and Assessment Procedures: Establishing rigorous auditing and assessment procedures for security protocols and technologies is vital. This ensures the security framework remains effective and adaptable to emerging threats.
- Data Analysis and Reporting: Analyzing security incident data and reporting findings to relevant stakeholders can provide valuable insights to improve security protocols. This process allows for continuous improvement and ensures the framework remains robust and effective.
- Feedback Mechanisms: Implementing feedback mechanisms to gather input from TSA staff, passengers, and other stakeholders is crucial. This will provide insights into areas for improvement and address any gaps in security protocols.
Hierarchical Structure of Potential Countermeasures
| Level | Countermeasure Category | Details |
|---|---|---|
| 1. Prevention | Improved Access Control Systems | Biometric authentication, threat assessments, advanced access control |
| Enhanced Surveillance Systems | Advanced video analytics, thermal imaging, redundant camera coverage | |
| Robust Background Checks | Comprehensive screening, data analysis of applicants | |
| 2. Detection | Advanced Threat Detection Technologies | Sensors, scanners, X-ray, millimeter wave imaging |
| Predictive Analytics | Historical data analysis, identification of potential threats | |
| Automated Threat Assessment Systems | Integration of data sources, real-time threat analysis | |
| 3. Response | Enhanced Training Programs | Continuous professional development, simulated exercises, expert-led modules |
| Continuous Monitoring and Evaluation | Auditing, data analysis, feedback mechanisms |
Case Study Comparison
The Nashville TSA security breach, a concerning incident, prompts a crucial examination of its place within the broader landscape of security breaches. Understanding similarities and differences with past events illuminates potential trends and weaknesses in security protocols, informing the development of more robust preventative measures. This comparison also reveals the evolving regulatory environment surrounding airport security and the impact on public trust.
Comparative Analysis of Security Incidents
Examining similar security breaches provides valuable context for understanding the Nashville incident. Comparing incidents reveals common threads and helps identify potential systemic vulnerabilities. This comparative analysis reveals the multifaceted nature of security challenges, highlighting the need for comprehensive and adaptable security strategies.
Similarities and Differences
Numerous security incidents share similarities with the Nashville breach, often involving human error, inadequate security protocols, or a combination of factors. Differences arise in the specific circumstances, the scale of the impact, and the response strategies employed. For example, while some incidents might involve unauthorized access, others might stem from internal failures or malicious intent. The severity of impact also varies, from minor disruptions to major crises, reflecting the complexities of risk assessment and mitigation.
Common Threads in Security Breaches
Several recurring themes emerge from security incidents, regardless of their specific nature. These recurring patterns highlight weaknesses in existing security frameworks and emphasize the importance of proactive vulnerability assessments. These threads include a lack of comprehensive security awareness training, insufficient staff oversight, and inadequate access control mechanisms. Additionally, a lack of robust contingency plans and inadequate communication protocols are frequently identified as contributing factors.
Regulatory Environment Surrounding Airport Security
The regulatory environment surrounding airport security is complex and multifaceted, reflecting a constant effort to balance safety, efficiency, and public convenience. Various regulations govern security procedures, screening protocols, and staff training, aiming to maintain a high level of security. This framework, however, is constantly evolving, responding to new threats and technological advancements.
Table of Comparable Security Breaches
This table summarizes key features of comparable security incidents, illustrating the scope and impact of these events. Understanding past incidents provides critical insights into the effectiveness of existing security measures and the need for continuous improvement.
| Incident | Location | Date | Impact | Key Factors |
|---|---|---|---|---|
| Nashville TSA Security Breach | Nashville International Airport | [Date of Incident] | [Detailed Impact Assessment from previous section] | [Factors from previous sections] |
| [Example Incident 1] | [Location] | [Date] | [Impact] | [Key Factors] |
| [Example Incident 2] | [Location] | [Date] | [Impact] | [Key Factors] |
Wrap-Up
The TSA security breach in Nashville highlighted critical weaknesses in existing protocols. While the investigation and immediate response are commendable, the incident underscores the urgent need for comprehensive security audits, robust cybersecurity training, and technological advancements. Lessons learned from this event can help prevent similar breaches in the future. A comparison with past security incidents further underscores the importance of proactive measures.
Query Resolution
What were the immediate consequences of the breach for travelers?
The immediate impact on travelers varied, ranging from inconvenience to heightened anxiety. Some flights were delayed, and additional security checks were implemented. The breach undoubtedly caused a level of concern and disruption.
How did the media cover the TSA security breach in Nashville?
Media coverage played a significant role in shaping public opinion. Different outlets presented varying perspectives, some focusing on the severity of the incident, others on the response from the TSA. A table comparing the different media outlets’ coverage would provide further insight.
What are some preventative measures to reduce the risk of similar security breaches?
Preventative measures include enhanced training for TSA personnel, regular security audits, and potential technological advancements in airport security systems. These proactive steps can strengthen the security infrastructure and deter future attacks.
What are the potential long-term implications for air travel in the region?
The long-term implications include potential adjustments to security protocols, increased scrutiny of security measures, and adjustments to public perception. The event likely impacted public trust and confidence in the TSA.

